Fraud Prevention and Personal Security, with Robert Siciliano
| A service person who takes your credit card out back to charge it can simply clone that card. | |
| |
 | How common is identity theft? |
 | Identity theft affects as many as 12 million people in the US every year. Everything from simple credit card fraud to complete bank takeover is costing people and businesses billions of dollars annually. |
 | What are some of the ways that identity thieves use to gain unauthorized access to others’ personal information? |
 | A service person who takes your credit card out back to charge it can simply clone that card. An individual or employee may receive an email that at a glance appears to be from a human resources department, but is in fact a fake email designed to get the employee to click links and spill personal information or company data. |
 | What are the first signs that someone has stolen your identity? |
 | When bill collectors call to collect for products and services that you never purchased, you certainly have a problem. Sometimes people even get arrested for crimes they didn't commit.
When a major corporation finds out that their data has been stolen, that's often a sign of employees making mistakes and providing criminals with backdoor network access. |
 | What should people do if they suspect that their identity has been compromised? |
 | I am a big believer in identity theft protection that has a restoration feature. Consider getting a "credit freeze.” It is also essential that users change up their passwords and have a different password for each critical account. |
| Too many people make the same mistakes every day such as using the same mundane easy-to-guess password for all of their critical accounts. | |
| |
 | What are the most important steps individuals and businesses can take to protect their information? |
 | It all begins with cyber security smarts. Too many people make the same mistakes every day such as using the same mundane easy-to-guess password for all of their critical accounts. If one account is compromised that means all critical accounts will be compromised because the criminal will simply enter the same username and the same password into multiple critical accounts.
In addition to that, keep your devices updated; make sure you have updated antivirus software, updated browsers, and updated operating systems. |
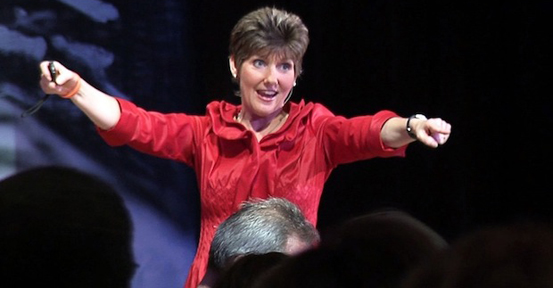
 | What is the difference between security awareness and security appreciation? |
 | Ongoing awareness training is failing everywhere we see it. We continue to see so many data breaches simply due to a lack of security appreciation which contributes directly to poor security awareness.
Security awareness certainly is a fundamental aspect of keeping employees trained to prevent data breaches. However "awareness" is a head based intellectual understanding of a concept – and that doesn't affect a person's behavior or performance. "Appreciation," on the other hand, is a heart based emotional connection to someone or something that effectively changes a person's behavior and gives them a deeper sense of understanding. This type of training actually solves security problems. |
 | What can organizations do to foster a culture of security appreciation? |
 | Companies need to engage in security awareness training but they also must jump-start that training by infusing it with security appreciation events. This means bringing in a qualified practitioner that gets into the hearts and minds of the participants. This is done by engaging in effective dialogue, encouraging Q&A that affects the participants’ personal lives, and presenting heartfelt, real life, cutting edge, up-to-the-minute story telling. |
 | What are a few actions small businesses can take to prevent their website from getting hacked? |
 | Company information security practitioners have all the hardware and software they need at their disposal, but what they often lack is simulated phishing expeditions and ongoing appreciation and awareness training. |
| These devices are being deployed on to the marketplace without being effectively vetted for security flaws and vulnerabilities. | |
| |
 | Security-wise what weak spots does the Internet of Things present? |
 | These devices are being deployed on to the marketplace without being effectively vetted for security flaws and vulnerabilities. As a result of their software and sometimes hardware, they can be breached wirelessly, which ultimately infects a person's mobile phone, laptop, or desktop with malware. |
 | How can individuals and companies using IoT technology protect themselves from hackers? |
 | It is essential that these devices are properly updated with the latest software and firmware to keep them secure. Sign up for manufacturer alerts for software updates. |
| In almost all of the mass shootings we've seen there was someone in the shooter’s life that recognized the bad intentions of the individual. | |
| |
 | Currently, one of the biggest concerns in the U.S., and other developed countries as well, are mass shootings or other forms of violent attacks in public places. Could you discuss your idea of “crowdsourcing security” and how ordinary individuals can help prevent future tragedies? |
 | Unlike most other countries, America is fanatical about firearms. We have an unhealthy celebration of guns. The ease of access for people with bad intentions will continue to result in tragedy unless we tighten up who has access and how. If an American were to have a conversation with anyone from Europe or Asia, they'd be stunned how difficult it is to get a gun in other parts of the world. While these words may not please firearm advocates there is undeniable truth in them.
However, since the gun lobby has the majority of control we must focus on education, awareness, and appreciation. Citizens should heed the Department of Homeland Security's motto: "If you see something, say something". This means if something doesn't seem right with someone then you have a duty to report it to someone in authority who can potentially intervene. In almost all of the mass shootings we've seen there was someone in the shooter’s life that recognized the bad intentions of the individual. Being proactive and intervening are absolutely critical. Finally, active shooter training - how to respond to an individual who is actively engaged in killing or attempting to kill people in a confined and populated area - is becoming an essential part of security awareness and appreciation training. To bring Robert Siciliano to your organization, please contact Michael Frick at: Mike@Speaking.com |